Do I Need a Firewall in the Cloud?

This blog series will cover architecture decisions that should be considered when migrating to the cloud. This series is written by a team of consultants that have worked with all walks of life in the cloud, from Fortune 50 enterprise to the “born in the cloud” startups, from FinTech to the retail industry. If there is a particular architecture decision or technology stack that you would like to series on, please leave us feedback in the comments section!
Do I need a firewall in the cloud?
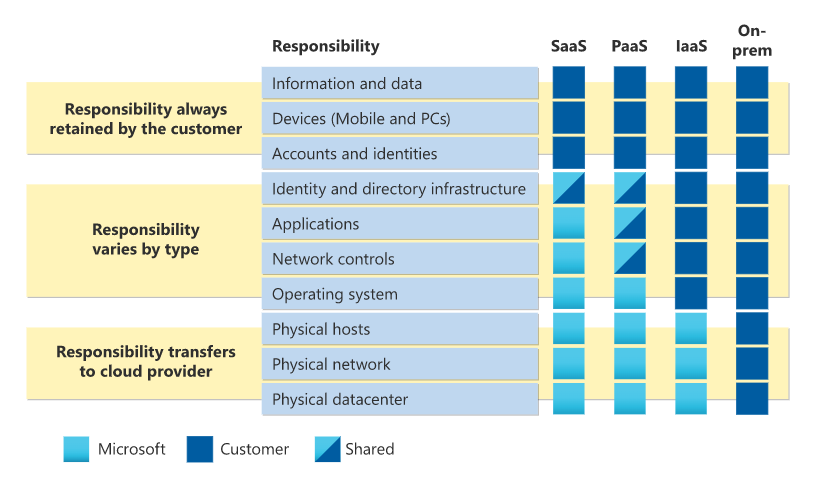
By embarking on this journey to the cloud, you will be extending your network perimeter to the cloud, meaning it will no longer be at the Internet circuit into your data center. Keep that in mind. All major cloud service providers will tell you there is a responsibility model. Below is great outline from Microsoft on this model.
From <https://docs.microsoft.com/en-us/azure/security/fundamentals/shared-responsibility>
Spoiler alert: GCP and AWS look very similar, if not identical. This means that you, the customer, have skin in the game as well. The reality is, CSPs knew that firewalls were necessary. As a result, not only did they make their own cloud native firewalls (Azure and AWS both have cloud native firewalls as PaaS offerings), but you will notice in both the AWS and Azure architecture diagrams that there is typically a “security hub” for traffic inspection and Internet ingress/egress. If you have been working in this industry long enough, more than likely, you have heard of “security in layers.” This is a layer. Notice that information and data are all a customer responsibility, so, to answer the question… Yes, you absolutely need a firewall in the cloud.
Okay, so I need a firewall, do I go cloud native or third party?
Great question! Short answer: whatever works for you.
Long winded version: Gather requirements for your firewall and the duties that it will have.
Here are some examples:
- Deep-packet inspection
- DNS filtering
- Connectivity to each branch office (maybe your branches have a firewall/router today that is SD-WAN capable)
- SSL unwrapping and inspection for all traffic incoming to the environment
- VPN concentrator for remote connectivity into the environment
- Security stack for another cloud (e.g. firewalls are deployed in AWS but you want them to inspect your traffic from Azure)
- Expected traffic throughput
- SLA committed to the business
- Operation familiarity managing a platform
- Control ingress and egress traffic into the cloud and/or on premises
Once the requirements are gathered and you know what features or benefits you are after, it is decision time. The longer the list of requirements gets, the more and more swayed to third party you probably went, which is normal. Cloud native firewalls are extremely hard to beat from a pure cost perspective, but you will be very limited to what you can implement with them. If there was a single variable that I would weigh the most in this equation, it would be the supporting team’s familiarity with the platform.
The cloud, the final frontier. Are you boldly going where no human has gone before? No…
The reality of migrating to the cloud is that there are several organizations that have migrated workloads, even data centers, to the cloud. That said, there have been a lot of lessons learned along the way, and hopefully this helps you learn from those lessons.
The ivision Cloud Team is equipped with the tools, experience and expertise to help your business make the best decisions for your personalized cloud needs. To get started, share your information at the link below and we’ll be in touch!



